Dolch PAC 64
The Dolch PAC 64 is a portable, rugged Pentium-powered PC from the mid 1990s. It was usually used (and can usually be found on eBay) as a "portable network sniffer" complete with multiple network cards supporting multiple media types.

The Dolch PAC 64 is a portable, rugged Pentium-powered PC from the mid 1990s. It was usually used (and can usually be found on eBay) as a "portable network sniffer" complete with multiple network cards supporting multiple media types.

I've been using an OpenBSD laptop as my workstation a lot more lately, probably because most of my hardware just works now and I don't have to think too much about it. The touchpad works when I touch it, I can be confident that when I close the lid, the laptop will fully suspend and then fully resume again when I open it, WiFi works all throughout my house (although it's not terribly fast), and my web browser is fast and stable. What amazing times we live in.
In the past, one thing that frequently kept me going back to my Mac, aside from iOS and Android development, was 1Password. I have a ton of logins for websites and servers, and because my browsers are all configured to clear cookies for most websites after I close their tabs, I need frequent access to passwords synced across my laptops and phones, and 1Password has great apps for all of those except OpenBSD.
ThinkPads have sort of a cult following among OpenBSD developers and users because the hardware is basic and well supported, and the keyboards are great to type on. While no stranger to ThinkPads myself, most of my OpenBSD laptops in recent years have been from various vendors with brand new hardware components that OpenBSD does not yet support. As satisfying as it is to write new kernel drivers or extend existing ones to make that hardware work, it usually leaves me with a laptop that doesn't work very well for a period of months.
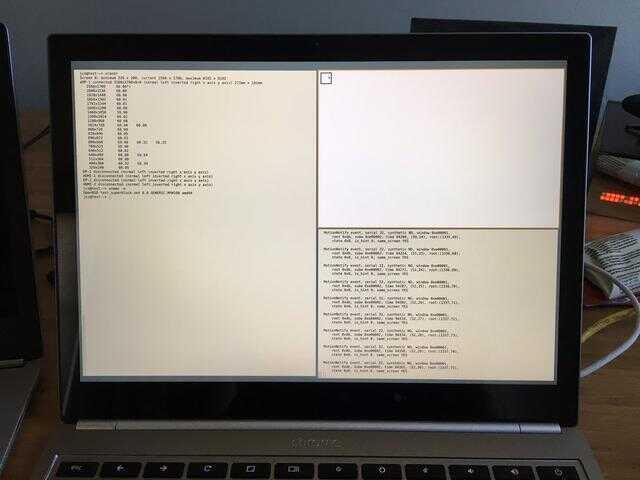
After exhausting efforts trying to debug the I2C touchpad interrupts on the Huawei MateBook X (and other 100-Series Intel chipset laptops), I decided to take a break and use something with better OpenBSD support out of the box: the fifth generation Lenovo ThinkPad X1 Carbon.

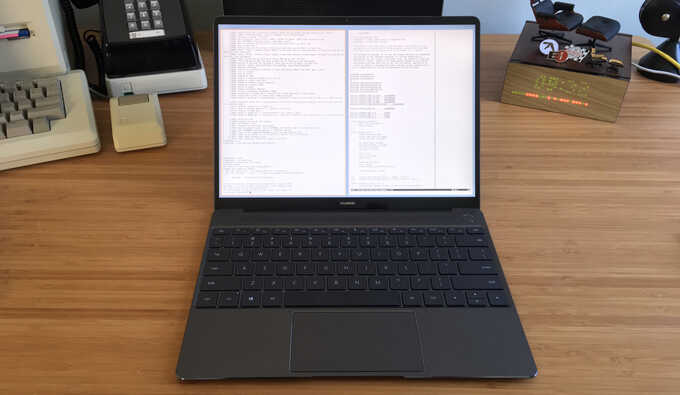
The Huawei MateBook X is a high-quality 13" ultra-thin laptop with a fanless Core i5 processor. It is obviously biting the design of the Apple 12" MacBook, but it does have some notable improvements such as a slightly larger screen, a more usable keyboard with adequate key travel, and 2 USB-C ports.
It also uses more standard PC components than the MacBook, such as a PS/2-connected keyboard, Intel WiFi card, etc., so its OpenBSD compatibility is quite good.

For the majority of the past five years, Pushover has run on one physical OpenBSD server. It does have a hot spare hosted with another company in another part of the country, but usually everything has been served from just one machine at a time. Its MariaDB database is replicated in a master-master configuration over a secure tunnel between the servers so that either node can become active at any time.
When I wanted to take the primary server down for upgrades or the server's
network provider was having routing troubles, I would update DNS for various
pushover.net entries to point at the other server's IPs where all of the
components were already running.
Within seconds, traffic would start hitting the secondary server and within a half
hour, everyone would be using it, allowing me to take the primary server offline
as long as I needed.
Back in 2015, I created a BBS for Lobsters that worked in a web browser via WebSockets. After getting an old Mac earlier this year, I wanted a way to access the BBS from the Mac as natively as I could. Adding telnet and SSH frontends to the BBS was not too difficult, but being able to login from my Mac took a bit of work.
In January I got a Macintosh 512Ke on eBay and spent some time fixing it up. The screen would occasionally flicker and shut off, but banging on the side of the case would sometimes bring it back. Some research pointed me to the analog board needing some capacitors replaced, which has completely solved the problem.
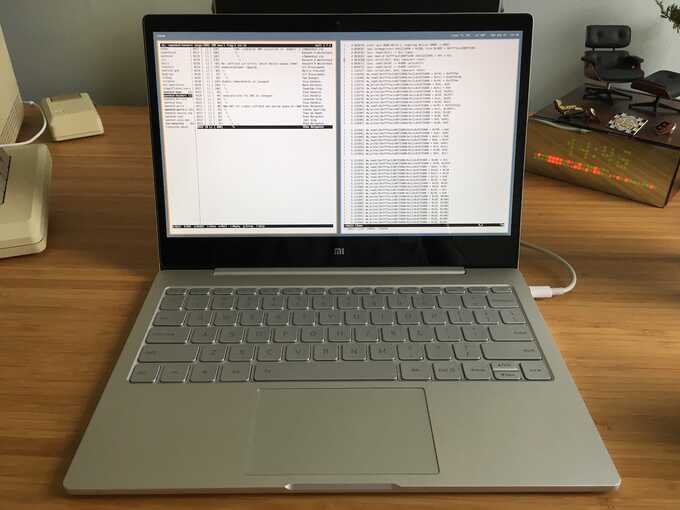
The Xiaomi Mi Air 12.5" is a basic fanless 12.5" Ultrabook with good build quality and decent hardware specs, especially for the money; while it can usually be had for about $600, I purchased mine for $489 shipped to the US during a sale.
Introduced in iOS 9, Universal Links allow iOS developers to claim ownership of domain names (including wildcards) that can be processed by that developer's iOS app. When an iOS user taps on a link to a URL of that domain name in any app, such as Safari or Mail, and the user has that 3rd party app installed, that 3rd party app is immediately launched to service the URL.
For web browsing apps on iOS that route traffic through VPNs or Tor, this feature can cause traffic to be sent outside of the VPN/Tor network without warning. For instance, if one has the eBay app installed and taps on this link from within Safari or any other web browsing app on iOS, the eBay app will be opened to load that auction page.
I recently had access to a Surface Pro 4 and tried to boot OpenBSD on it. It did not go well, so I am just putting this here for posterity.
The 2016 Surface Pro 4 is basically just a keyboard-less x86 (Core i5 on the model I had) tablet with some tightly integrated (read: not upgradeable) components. Its optional Surface Type Cover is just a USB-attached keyboard and trackpad, which magnetically secure to the bottom of the device.
I've been using an 11" MacBook Air as my primary computer for six years. It's a great computer that satisfied a lot of requirements I had for a laptop: thin, lightweight, small form factor, excellent keyboard and touchpad, mostly silent, but not an Atom or Core M processor.
I've done a lot on this little computer, like compiling and maintaining an Android ROM, writing the Rails, iOS, and Android apps for Pushover, creating Lobsters, recording and editing 40 episodes of Garbage, and lots of OpenBSD development.
The Chromebook Pixel LS (2015) has an Intel Core i7 processor (Broadwell) at 2.4 GHz, 16 GB of RAM, a 2560x1700 400-nit IPS screen (239ppi), and Intel 802.11ac wireless. It has a Kingston 64 GB flash chip, of which about 54 GB can be used by OpenBSD when dual-booting with a 1 GB Chrome OS partition.
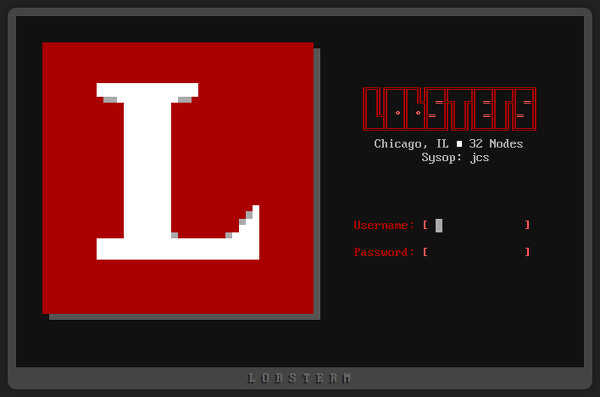
Although it fooled nobody, yesterday for April Fools' Day, Lobsters users that normally saw a boring list of story titles and links were greeted with a BBS-style interface to the site complete with story and comment browsing, private message reading and sending, and a multi-user chat area.
The BBS remains active at
https://lobste.rs/bbs (you can login as
"guest").
I recently activated a new dedicated server that came preinstalled with Linux, as the hosting provider didn't support OpenBSD. Since they also didn't provide an IP-based KVM without purchasing a dedicated hardware module (though most of the IP-KVMs I've used recently require interfacing with some terrible Java-based monstrosity anyway), I needed a way to remotely install OpenBSD over the running Linux server.
I spent a week in Toronto, Canada attending the OpenBSD t2k13 hackathon hosted at the University of Toronto. While these events are put on every year in random places, I have not attended one since c2k7 in Calgary back in 2007. I tried to go to the Portugal hackathon last year but my travel plans got all screwed up.
I wrote about the technical details of what I accomplished at this event at the OpenBSD Journal so I won't duplicate it here, but it was a fairly productive week for me. I remember at c2k7 I didn't really have much to work on and felt out of place but this time I had more things to do than I had time.
It's been a little over 6 months since I released Pushover, the notification service with Android and iOS apps. I've been asked to post an update on how things have been going since then.
Shortly after the initial release, I received some great feedback from Chad Etzel, one of the creators of Notifo, the notification service that I used until it was shut down (which prompted me to create Pushover in the first place). Chad asked for Pushover to support sending messages with URLs that can open external apps, and Pushover soon gained supplementary URL support which required changes in the API and on both Android and iOS apps.